
Threat Hunting: An Overview
Threat Hunting: An Overview
Threat hunting is a proactive process where security teams actively search for indicators of compromise (IoCs) that signal potential threats within an organization’s network. This process helps achieve the detection and analysis phases of the incident response (IR) process, ensuring that threats are caught early before they cause significant damage.
Some key IoCs (Indicators of Compromise) include:
- Account lockout: Often due to brute-force attacks or multiple incorrect password attempts, indicating malicious access attempts.
- Concurrent session usage: If a user has multiple active sessions, especially from unusual locations, it might indicate credential compromise.
- Blocked content: An alert triggered when malware or an attacker tries to access content that has been blacklisted by the organization’s filters.
- Impossible travel: A user logging in from two geographically distant locations in a short time span is a strong indicator of compromised credentials.
- Resource consumption: Abnormal usage of disk space, bandwidth, or memory may signal a compromise, especially when resource-heavy operations (like data exfiltration) occur.
- Resource inaccessibility: Files, systems, or services becoming unexpectedly unavailable might be the result of malicious tampering.
- Out-of-cycle logging: Unusual access times or unexpected system events can suggest suspicious activity, such as an attacker’s presence.
- Missing logs: Logs being wiped or tampered with can be an attempt by an attacker to cover their tracks.
These IoCs help threat hunters to pinpoint malicious activity early, allowing for swift incident response.
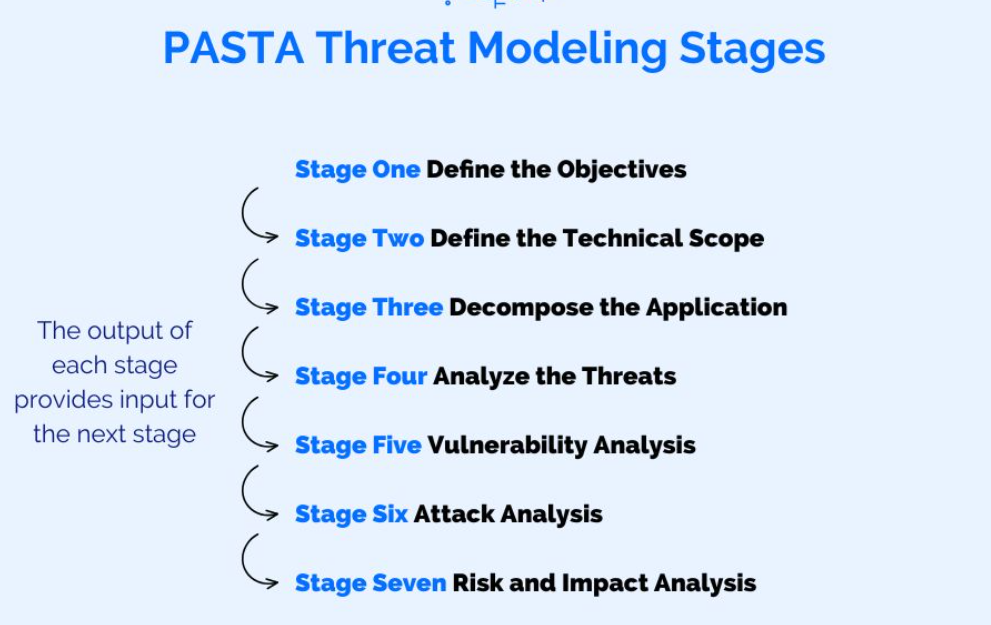
Step-by-Step Threat Hunting Using PASTA Framework
PASTA (Process for Attack Simulation and Threat Analysis) is a risk-centric threat modeling framework that provides a structured, step-by-step approach for threat hunting. It enables security teams to simulate potential attack scenarios and proactively identify threats. Here’s how you can perform threat hunting using the PASTA framework:
1. Define the Objectives (Stage 1: Define the Business Objectives)
The first step in threat hunting using PASTA is understanding the business context and objectives. This includes identifying the organization's critical assets, systems, and processes. Understanding the business goals helps prioritize which assets are most important to protect.
- Action: Identify the most critical assets to the business, such as customer data, intellectual property, or key infrastructure components.
2. Identify the Attack Surface (Stage 2: Define the Technical Scope)
In this step, the goal is to identify the systems, networks, applications, and endpoints that are part of the attack surface. This includes all potential entry points and vulnerabilities that an attacker could exploit.
- Action: Map out the organization's infrastructure, applications, and potential access points that could be exploited by attackers.
3. Decompose the Application (Stage 3: Application Decomposition & Attack Surface Analysis)
This stage involves breaking down the target systems or applications into their components and understanding how they function. It includes identifying trust boundaries, data flows, and dependencies.
- Action: Conduct a detailed analysis of the system's architecture, focusing on areas where data flows between trust boundaries (e.g., between users and servers).
4. Threat Modeling (Stage 4: Threat Analysis)
Once the attack surface is understood, you can begin threat modeling. This involves identifying potential threats and attack vectors based on the assets, attack surface, and business objectives. The goal is to simulate how an attacker might attempt to compromise the system.
- Action: Identify the most relevant attack vectors (e.g., phishing, lateral movement, privilege escalation). Simulate potential scenarios where these threats could be exploited.
5. Identify Vulnerabilities (Stage 5: Vulnerability and Weakness Analysis)
Next, the focus shifts to identifying vulnerabilities within the system. This could include technical vulnerabilities (e.g., unpatched software) or procedural weaknesses (e.g., poor password policies). Threat hunters look for both known vulnerabilities and new, emerging threats.
- Action: Use automated tools and manual methods to scan for vulnerabilities. Compare this against threat intelligence to identify which vulnerabilities are currently being exploited in the wild.
6. Attack Simulation (Stage 6: Attack Simulation)
In this step, security teams simulate attacks based on the identified vulnerabilities and attack vectors. This allows the organization to see how an actual attack might play out and which systems or processes are most vulnerable.
- Action: Use red teaming or penetration testing to simulate an attack. Observe how the system responds and identify weak points that need to be addressed.
7. Risk and Impact Analysis (Stage 7: Risk and Impact Analysis)
Finally, analyze the impact of potential attacks on the organization. This includes assessing both the technical and business impacts of an attack, such as data loss, service downtime, or reputational damage.
- Action: Prioritize remediation efforts based on the risk level and the potential business impact of each identified vulnerability or threat scenario.
Conclusion
Threat hunting using the PASTA framework is a powerful way to not only detect threats but also to simulate potential attack scenarios and understand their impact on your organization. By systematically identifying vulnerabilities and proactively addressing them, organizations can greatly reduce their risk of compromise. Regular practice and continual improvement of this process ensure that the IR team stays prepared and capable of handling new and evolving threats.
Featured links
Connect with us
Copyright © 2026